Credit: cottonbro studio / Platform
Credit: RDNE Stock project / Pexels
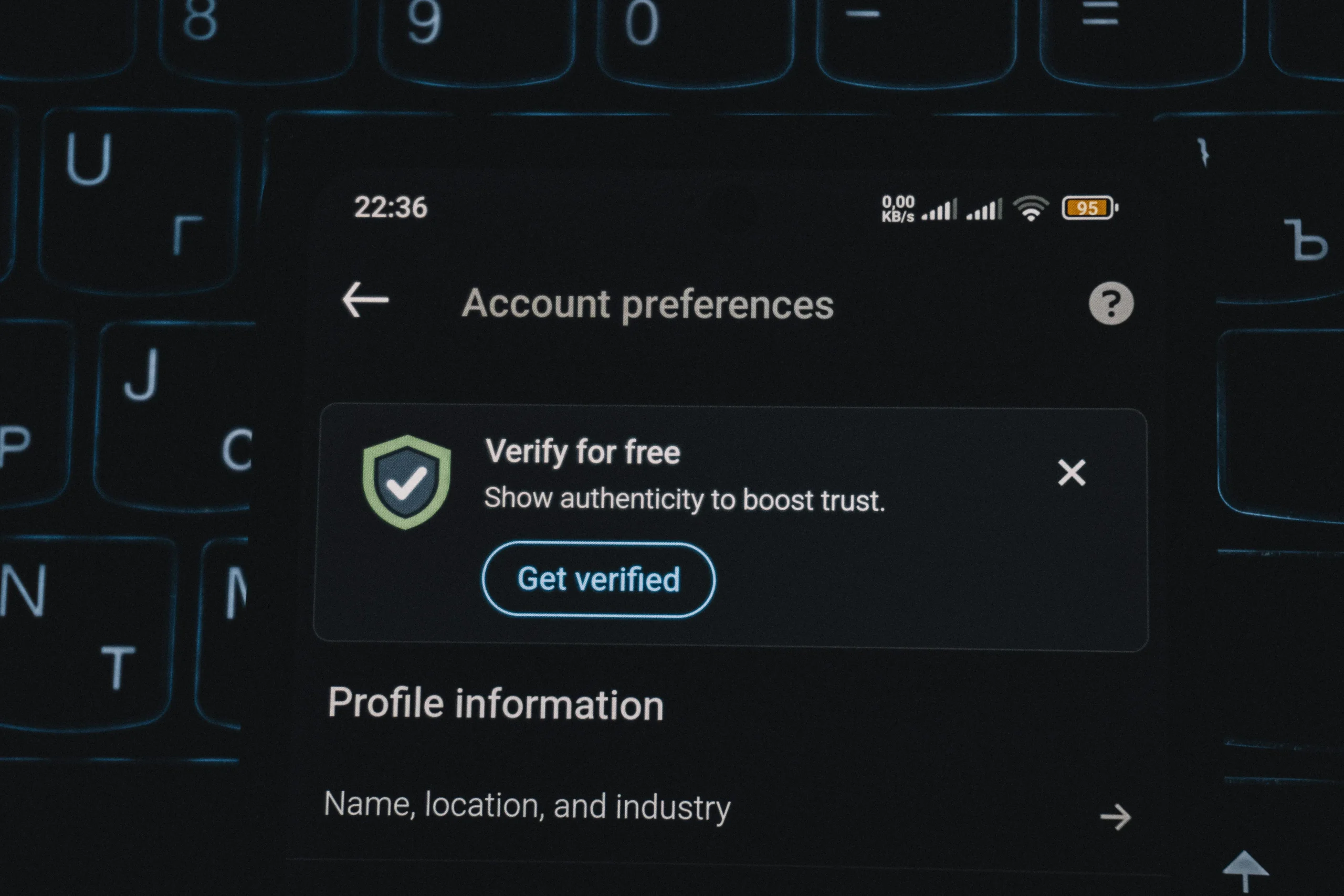
5. Why “Phone Apps Are Safer Than Websites by Default” Is Not Always True
Some users trust mobile apps more automatically than websites, assuming apps are always safer just because they are installed on a phone. In reality, apps still rely on permissions, account settings, stored sessions, and data collection practices that deserve careful review.
Mobile security professionals explain that an app may still request broad access to location, contacts, microphone, photos, or background activity. If users grant permissions without review, the convenience of the app can come with more privacy exposure than expected.
Experts recommend reviewing app permissions and privacy details rather than assuming installation alone equals safety. Trust should come from settings and behavior, not only from platform format.
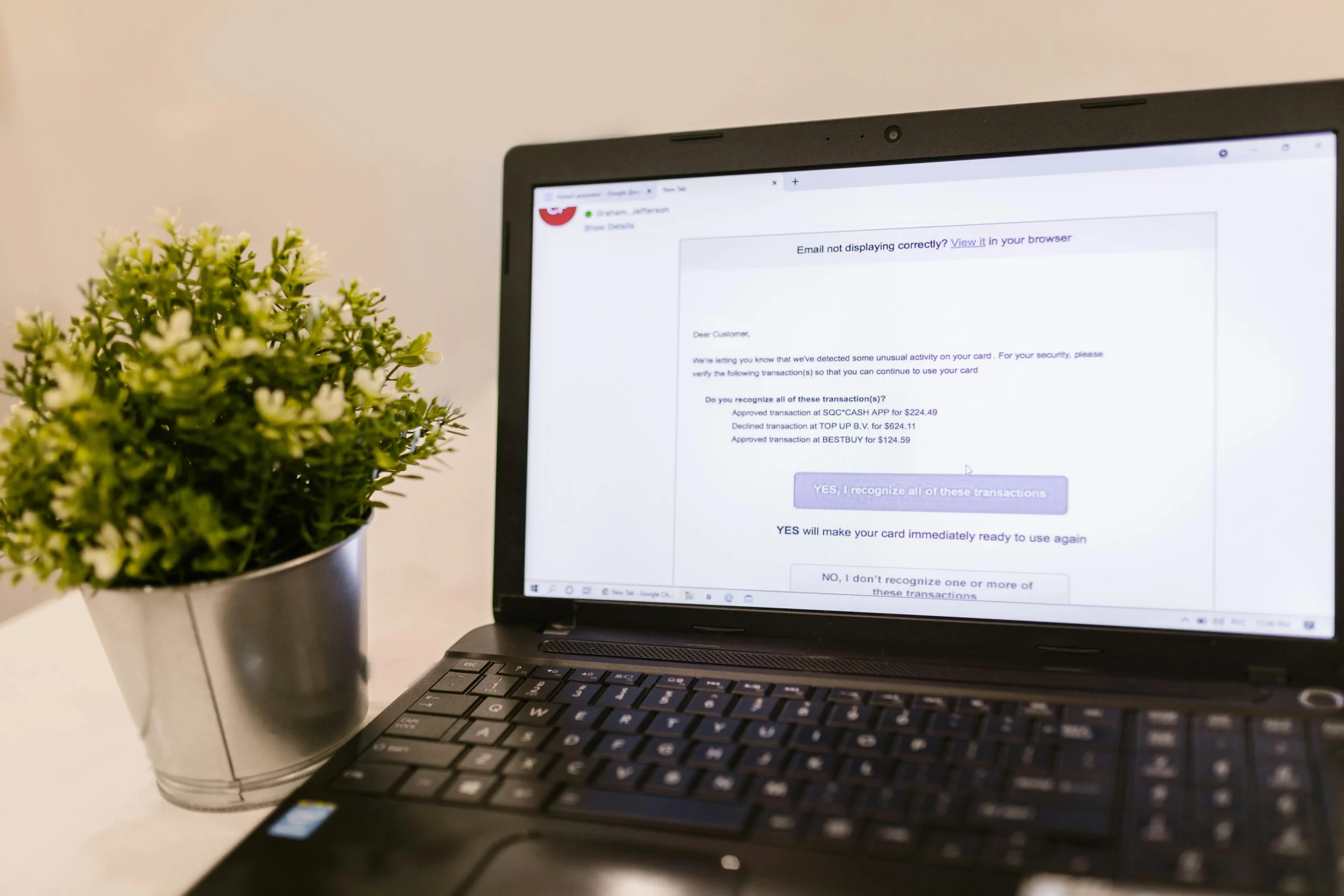
6. Why “Older Accounts Do Not Matter Anymore” Can Leave Personal Information Online
Users often ignore old accounts from shopping sites, forums, apps, or services they no longer use. The assumption is that if the account is forgotten, it no longer matters. In practice, abandoned accounts may still contain personal details, old payment history, saved addresses, or reused passwords.
Privacy specialists explain that older accounts can become weak points because they are reviewed less often and may still rely on outdated passwords or recovery methods. If an old service is exposed in a breach, the information may still be valuable to attackers.
Experts recommend reviewing unused accounts from time to time and removing or securing the ones that no longer serve a purpose. Internet safety facts often matter most in places users stopped thinking about long ago.
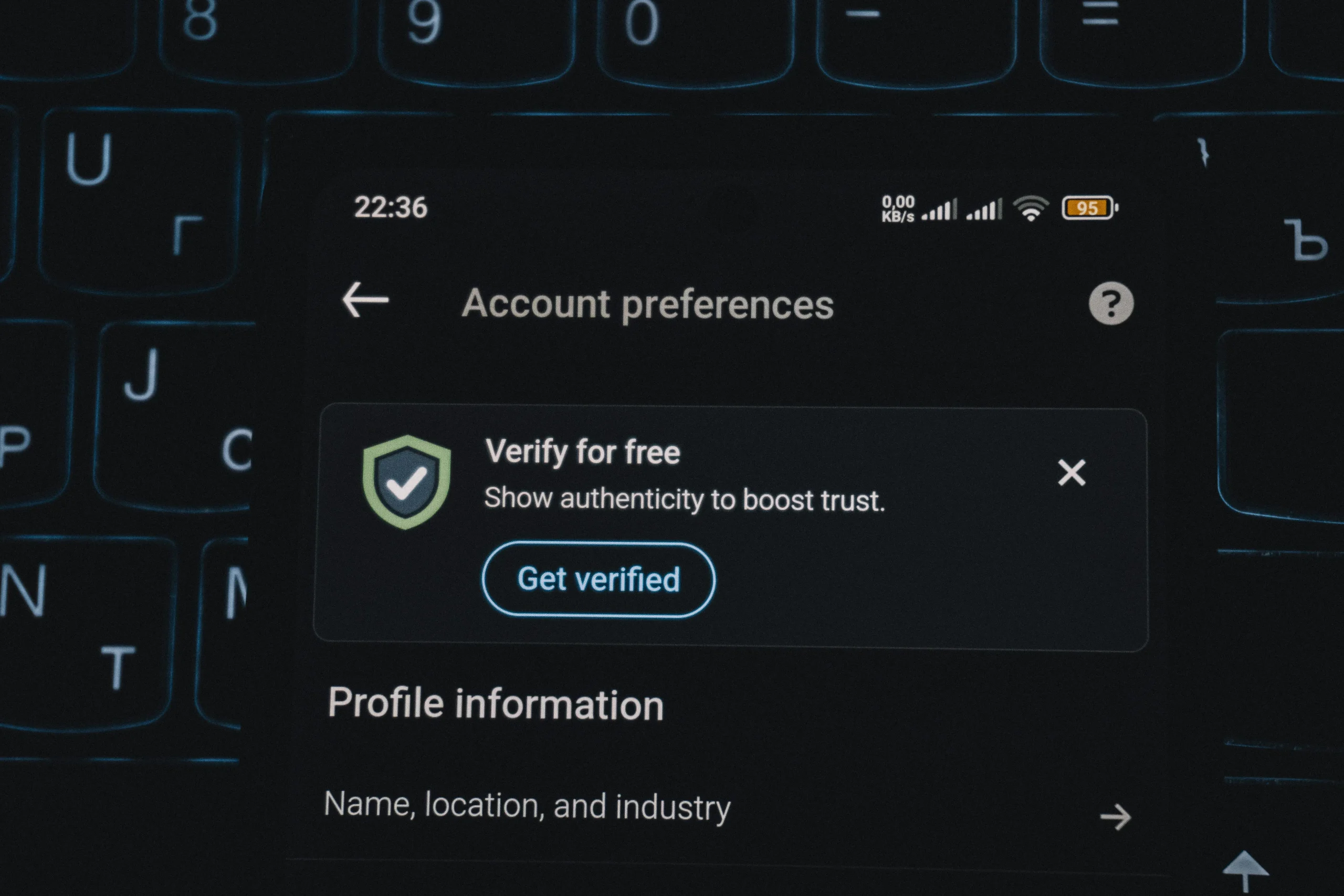
7. Why “Security Settings Only Need to Be Set Once” Is One of the Most Persistent Online Safety Myths
One of the most persistent online safety myths is the belief that security settings are a one-time task. In reality, apps change, browsers update, devices are replaced, and account services add new options or risks over time. A setup that felt strong last year may now be outdated or incomplete.
Cybersecurity researchers explain that good protection depends on review, not only setup. Passwords may need to be changed, devices may need to be removed from old sessions, permissions may need to be adjusted, and privacy settings may need another look after updates.
Experts recommend short regular reviews rather than rare major overhauls. A few minutes of routine checking often protects online accounts better than one large security effort that is never revisited.
Frequently Asked Questions
Q: What are online safety myths?
A: Online safety myths are common beliefs about digital protection that sound useful but may lead to weaker account or privacy habits.
Q: Why do online safety myths spread so easily?
A: Experts say they spread because they are simple, familiar, and often repeated without enough real testing or review.
Q: Is a strong password enough to protect an account?
A: No. Strong passwords help, but account safety usually improves most when extra login protection and careful scam awareness are also used.
Q: Are apps always safer than websites?
A: Not always. Apps can still collect broad data, keep old sessions active, and request permissions that deserve close review.
Q: How often should users review account safety settings?
A: A short review every few months, or after major updates or device changes, is often a practical habit.
Key Takeaway
Understanding common online safety myths can help users replace weak habits with more practical protection. Experts recommend combining strong passwords with extra login protection, reviewing old accounts, checking app permissions, and returning to security settings regularly instead of treating them as finished forever. Better online safety usually comes from steady habits, not from assumptions that only sound reassuring.
[INTERNAL LINKING SUGGESTIONS]
– Why Two-Factor Authentication Matters and How It Protects Online Accounts
– What Happens in a Data Breach and What Users Should Do Next
– How to Spot Phishing Emails Before They Put Your Accounts at Risk